Problem Statement :
This lab contains an SQL injection vulnerability in the product category filter. When the user selects a category, the application carries out an SQL query like the following:
SELECT * FROM products WHERE category = ‘Gifts’ AND released = 1
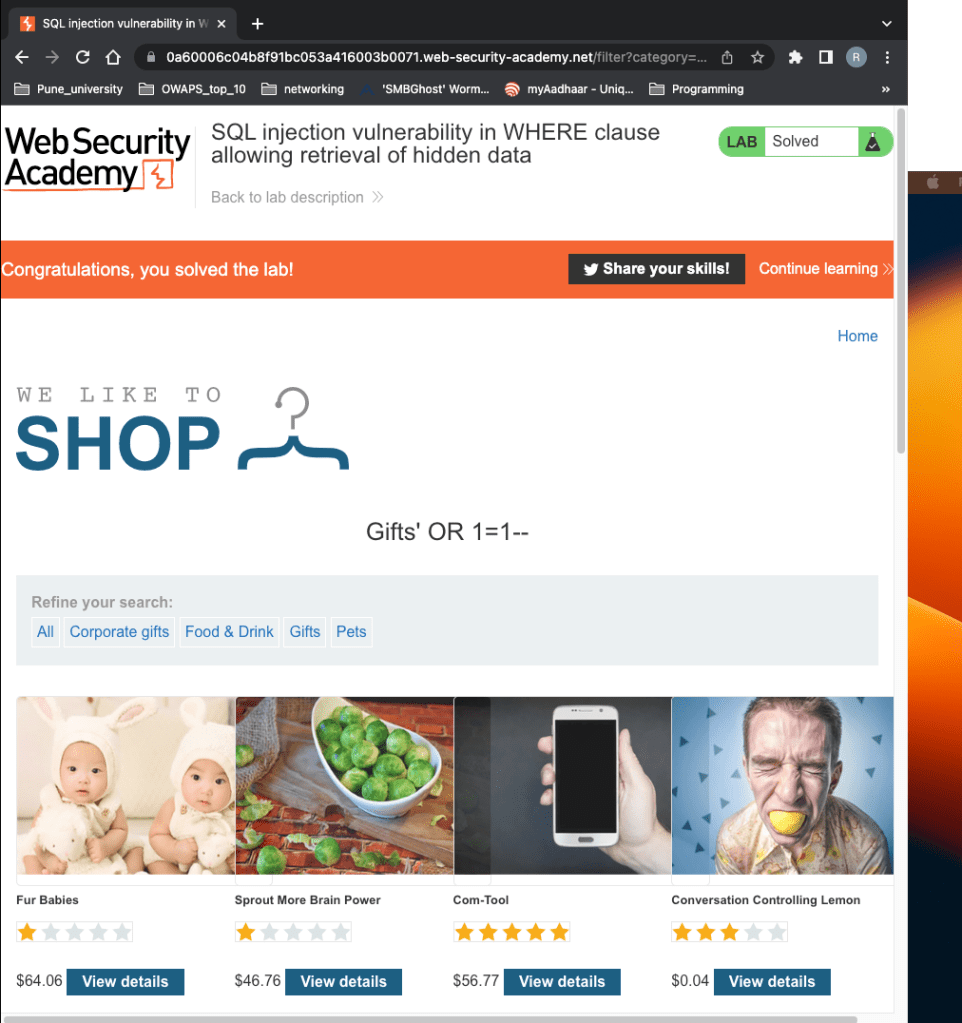
To solve the lab, perform an SQL injection attack that causes the application to display details of all products in any category, both released and unreleased.
Solution:
In order to solve this problem. First click on Gift’s menu to load all items under gifts.
The URL in address bar will be seen in this way.
https://0a60006c04b8f91bc053a416003b0071.web-security-academy.net/filter?category=Gifts
Next – The question is to display details of all products in any category, both released and Unreleased.
We modify the URL and enter this at the end of the URL.
‘ OR 1=1–
Explanation –
–> ‘ (This single quote we are ending the URL after gifts (which also means we are ending the query there) )
–> OR (We are adding another condition there to trick the database. We are saying OR
–> 1=1 (Which means 1 = 1 is always true. )
–> — (these 2 dashes are commenting out everything else after this) .
https://0a60006c04b8f91bc053a416003b0071.web-security-academy.net/filter?category=Gifts’ OR 1=1–
As you can see it says we have solved the lab. Because we are now able to see all the items there from all the category.
Leave a comment