In the rapidly advancing digital era, security vulnerabilities in popular platforms and protocols can have far-reaching consequences. Two recent discoveries—the Microsoft Teams vulnerabilities and a critical flaw in Convoc2—have stirred the cybersecurity community. This post explores these vulnerabilities, their potential impact, and how we can safeguard against them.

I’ve created an infographic illustrating the vulnerabilities in Microsoft Teams and Convoc2, along with their solutions.
Microsoft Teams Vulnerabilities: A Growing Concern
Microsoft Teams has become a central tool for collaboration in workplaces worldwide, making it a prime target for cyberattacks. Recent security investigations have uncovered several exploitable weaknesses:
1. Credential Harvesting via Malicious Links
Phishing campaigns often use trusted platforms to deliver malicious links. Attackers exploit users’ trust in Teams to send links leading to credential-stealing websites, bypassing traditional security measures.
2. Remote Code Execution (RCE) Flaws
Some vulnerabilities in Teams allow attackers to execute arbitrary code. Manipulated attachments, GIFs, or files with embedded exploits can compromise users’ systems if opened or viewed.
3. Privilege Escalation Through Misconfigurations
Improperly configured permissions in Teams environments may allow attackers to elevate privileges, accessing sensitive data or administrative functions.
How to Protect Microsoft Teams:
- Enable advanced threat protection: Use solutions designed for Teams to detect malicious links or files.
- Regular updates: Ensure that Teams is running the latest version to benefit from patched vulnerabilities.
- Educate users: Training employees to identify phishing attempts can significantly reduce risks.
- Restrict permissions: Limit user roles and access based on necessity.
Convoc2 Vulnerability: Weakening Secure Communications
Convoc2, a protocol designed for secure and efficient communication, has been identified with critical security flaws, posing risks to applications that rely on it.
1. Cryptographic Weaknesses
Poor key management in Convoc2 compromises data confidentiality. This flaw allows attackers to intercept and decrypt sensitive communications.
2. Token Replay Attacks
Authentication tokens used by Convoc2 are vulnerable to replay attacks, enabling attackers to reuse a valid token to gain unauthorized access to systems or sessions.
3. Denial-of-Service (DoS) Exploits
The protocol lacks mechanisms to limit request rates or handle malformed inputs, making it susceptible to DoS attacks that can disrupt services.How to Strengthen Convoc2 Security:
- Implement secure key exchange protocols and robust cryptographic standards.Add timestamp validation and expiration policies for authentication tokens to prevent replay attacks.Introduce rate limiting and anomaly detection to thwart DoS attempts.
The Bigger Picture: Cybersecurity Practices for All
The challenges with Microsoft Teams and Convoc2 remind us of the importance of proactive cybersecurity practices:
- Conduct regular security audits and vulnerability scans for all systems.
- Follow secure coding principles to minimize exploitable flaws during development.
- Encourage awareness training for employees and end-users to recognize threats.
Whether you’re managing an enterprise, developing protocols, or simply using these platforms, staying ahead of vulnerabilities is key to preventing exploitation.
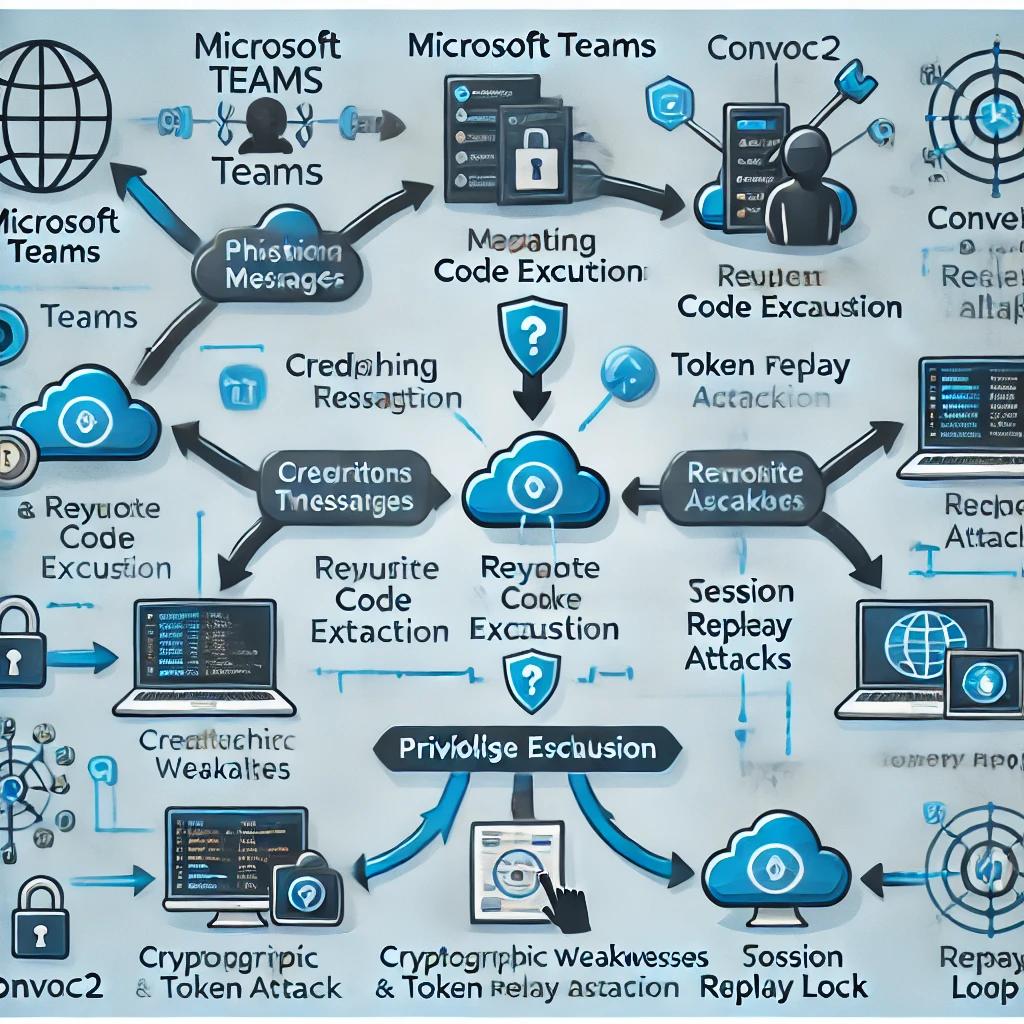
Here is an attack flow chart illustrating the exploitation process for vulnerabilities in Microsoft Teams and Convoc2. It highlights each step of the attack path with clear labels and visuals.
Conclusion
The recent vulnerabilities in Microsoft Teams and Convoc2 highlight the need for constant vigilance in cybersecurity. By understanding these threats and adopting robust defense strategies, we can collectively contribute to a safer digital environment.
What’s your take on these vulnerabilities? Have you encountered similar security issues in your environment? Share your experiences and join the conversation!
Leave a comment