Introduction
SSH key-based authentication is widely considered more secure than password-based login. However, security does not end at key generation. If a private SSH key is compromised and protected with a weak passphrase, it can often be cracked offline—leading to full system access.
In this blog post, we will walk through a realistic penetration testing scenario where an attacker has obtained a victim’s SSH private key and attempts to crack its passphrase using tools available in Kali Linux.
⚠️ This content is intended for educational and authorized penetration testing only.
Threat Scenario
Assume the following:
- You have gained access to a victim machine (Ubuntu)
- You successfully extracted an SSH private key (
id_ed25519orid_rsa) - The private key is passphrase-protected
- SSH password authentication may be disabled
- Your objective is to recover the passphrase and authenticate via SSH
This situation is commonly encountered during:
- Internal network pentests
- Post-exploitation phases
- CI/CD pipeline compromises
- Backup or misconfigured home directory exposure
Important SSH Concept (Common Misunderstanding)
To crack an SSH key passphrase:
- ❌ You do NOT need the public key
- ❌ You do NOT need access to the SSH server
- ✅ You only need the private key file
The attack is offline, meaning:
- No logs
- No rate limiting
- No detection from the target system
The passphrase protects the private key itself, not the SSH login process.
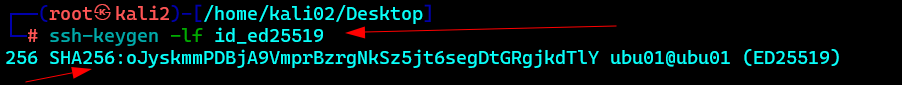
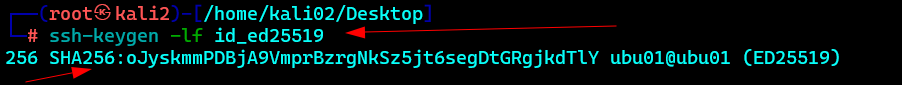
Step 1: Identify the Private Key Type
Before cracking, identify the key type:
file id_ed25519or
ssh-keygen -lf id_ed25519Common key types:
- RSA
- ED25519
- ECDSA
Step 2: Convert SSH Private Key to John Format
Kali Linux includes a tool called ssh2john, which extracts a crackable hash from the private key.
ssh2john id_ed25519 > sshkey.hashThis converts the encrypted private key into a format understood by John the Ripper.
Example output:
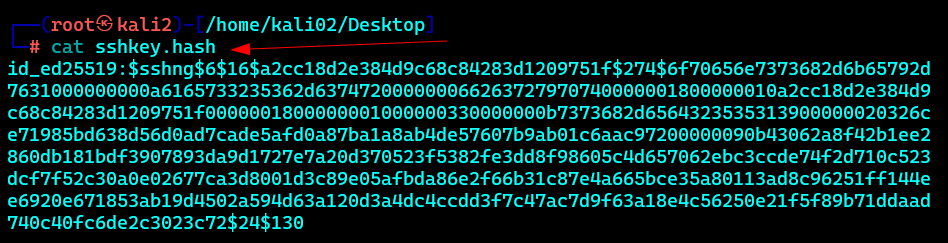
This is not a system password hash — it represents the private key passphrase hash.
Step 3: Crack the Passphrase with John the Ripper
Dictionary Attack (Most Effective)
john --wordlist=/usr/share/wordlists/rockyou.txt sshkey.hash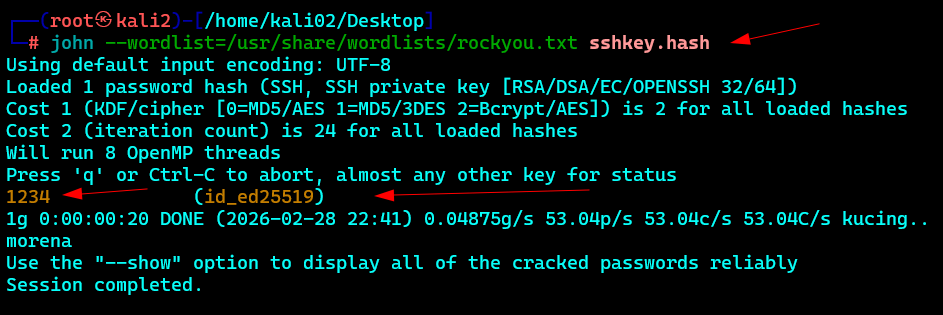
Dictionary + Rules (Recommended)
john --wordlist=/usr/share/wordlists/rockyou.txt --rules sshkey.hashBrute Force (Last Resort)
john --incremental sshkey.hashThe effectiveness depends entirely on passphrase complexity.
Step 4: Retrieve the Cracked Passphrase
Once John finishes:
john --show sshkey.hashExample output:
At this point, the private key is fully compromised.
Step 5: SSH into the Target System
Use the cracked private key:
ssh -i id_ed25519 ubu01@192.168.1.12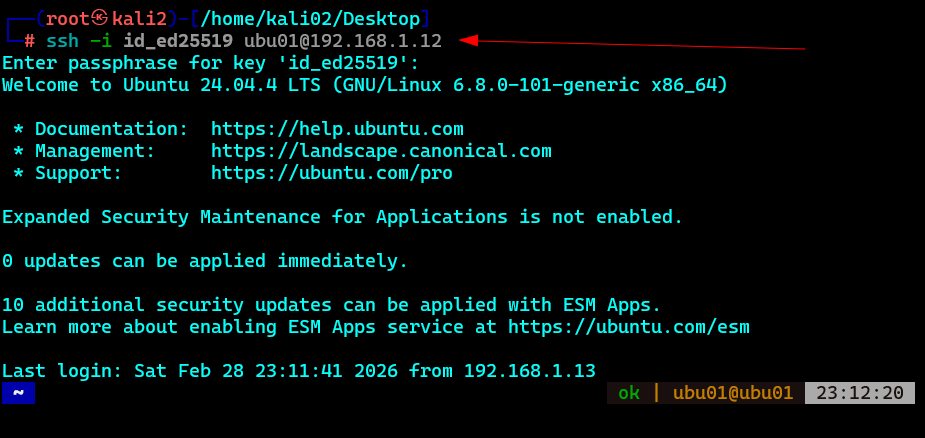
When prompted, enter the recovered passphrase.
Successful authentication confirms full user compromise.
Why This Attack Works in Real Environments
From real pentest experience:
- SSH keys are often reused across systems
- Passphrases are commonly:
- Weak
- Based on seasons, years, or company names
- Reused from login passwords
- Private keys are frequently found in:
- Backups
- Git repositories
- CI/CD runners
- Misconfigured home directories
Impact
If an attacker cracks an SSH private key passphrase, they gain:
- Persistent access
- Password-less login
- Potential lateral movement
- Access that often bypasses MFA
This is a high-impact finding in penetration tests.
Defensive Recommendations
To mitigate this risk:
- Use strong, unique SSH key passphrases
- Prefer hardware-backed keys (FIDO2 / YubiKey)
- Rotate keys immediately if exposure is suspected
- Enforce strict permissions:
chmod 600 ~/.ssh/id_* - Avoid storing private keys in scripts, repos, or backups
- Monitor SSH key usage and login patterns
Conclusion
SSH keys are only as strong as their passphrases and storage practices.
A stolen private key combined with a weak passphrase can be cracked silently and offline, leading to complete compromise.
For penetration testers, this technique is an essential post-exploitation skill.
For defenders, it highlights why key management hygiene is critical.
Refer to my Vlog @Scrollunlock :
Leave a comment