Problem Statement :
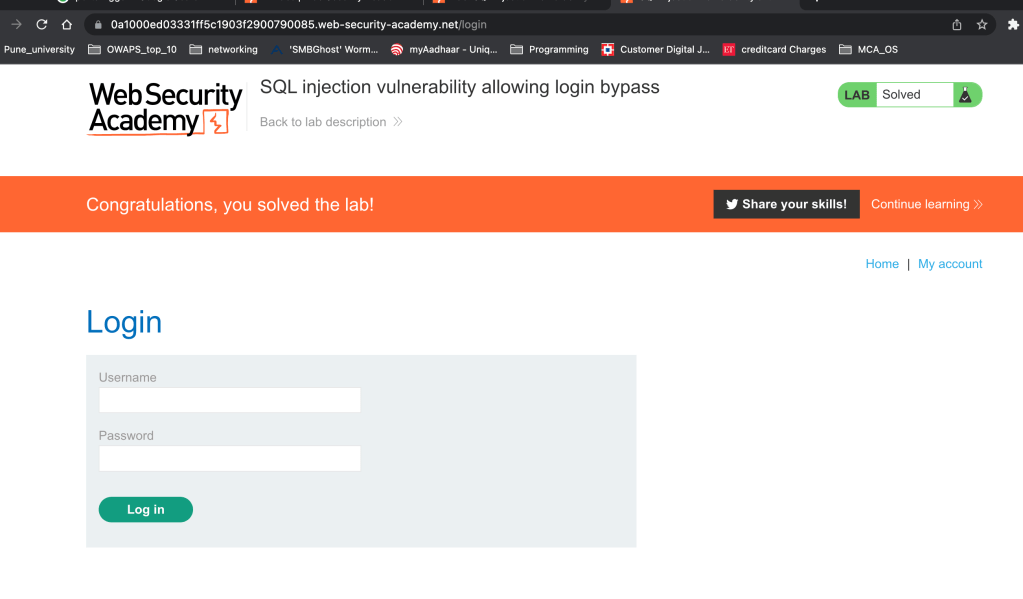
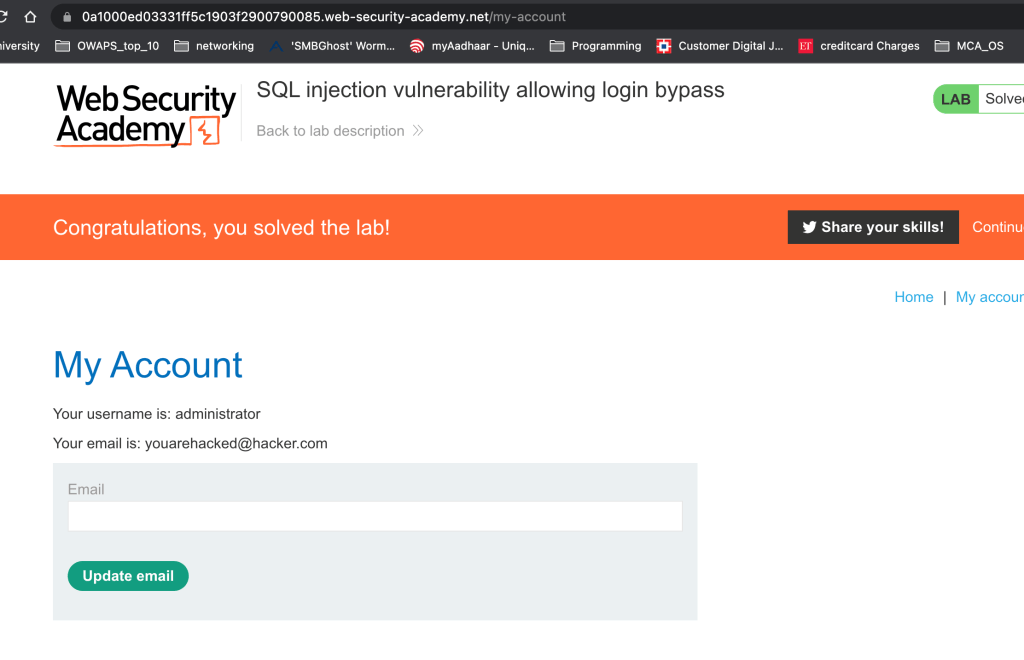
This lab contains an SQL injection vulnerability in the login function.
To solve the lab, perform an SQL injection attack that logs in to the application as the administrator user.
Solution:
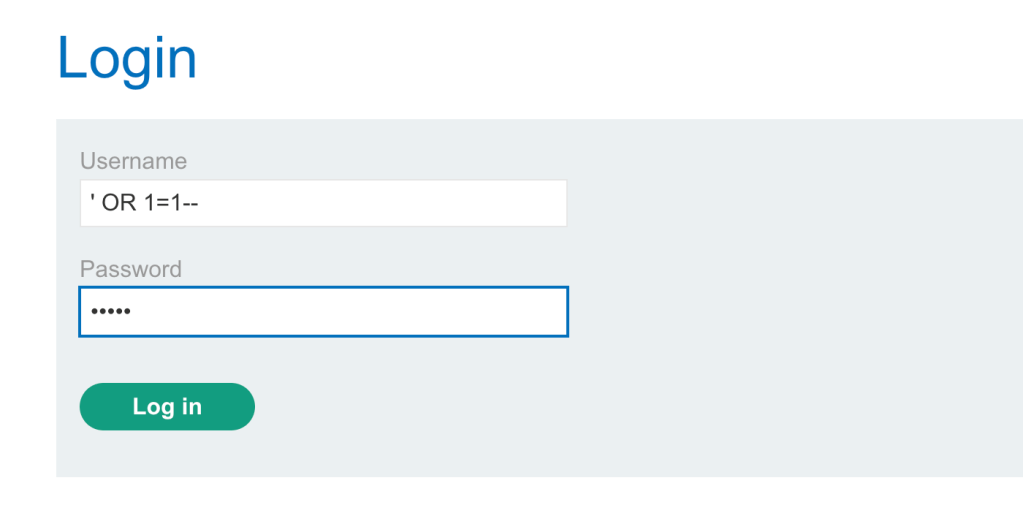
- Click MyAccount and it will show you the login page.
Next –
–> Type username as = ‘ OR 1=1–
–> type any password
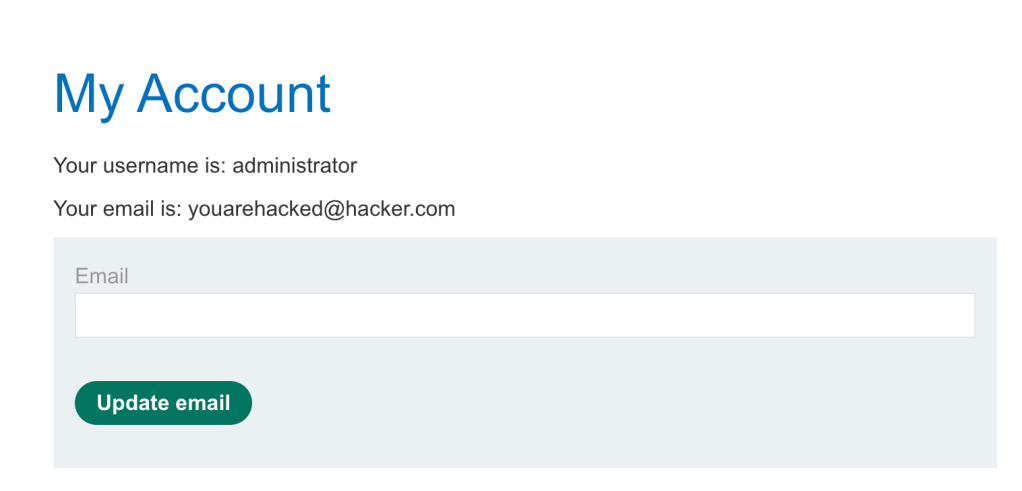
Next I am logged in
Understanding the Solution :
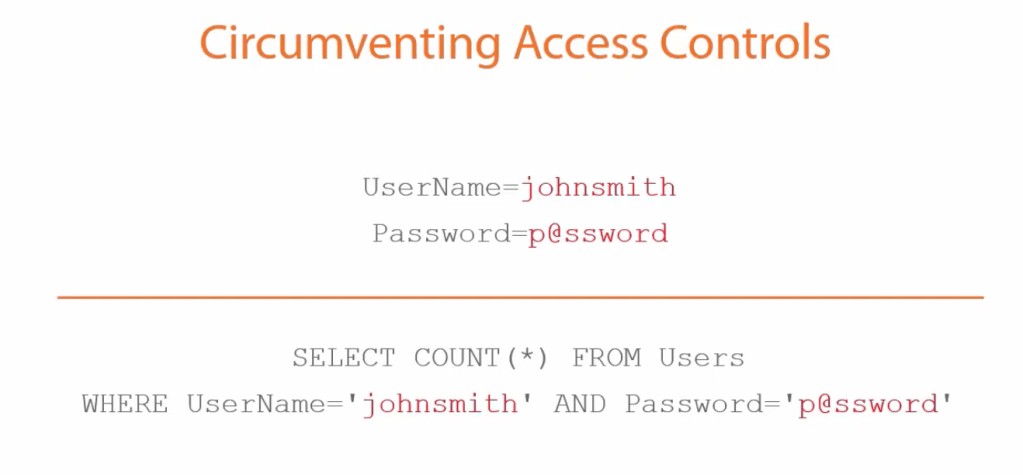
Understand this query – The reason it is doing SELECT COUNT (*) here is to check how many of them exist. It will just return integer 1 or 0
If the values are true it will log in the user.
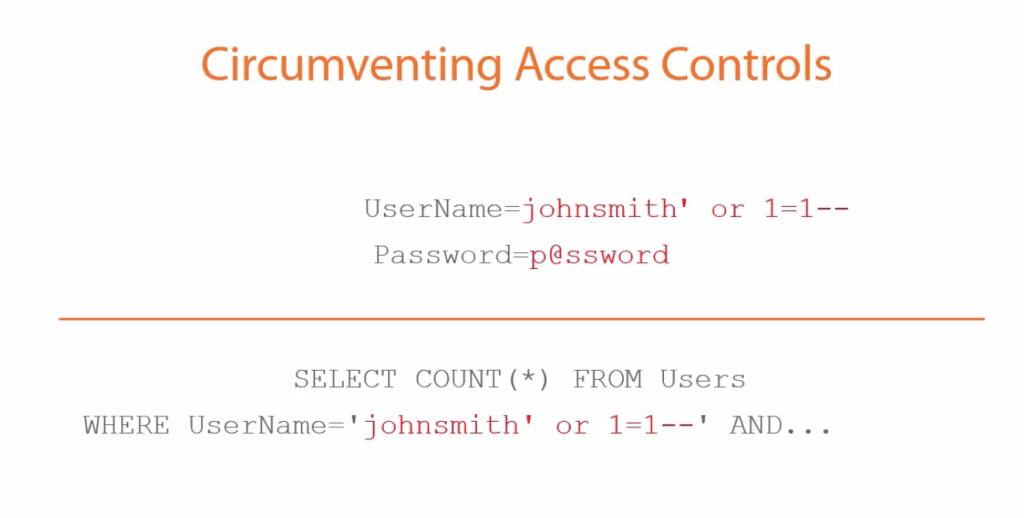
Lets add single quote and or 1=1 — at the end of the user name
UserName = Johnsmith’ OR 1=1–
This is how it looks in the query.
Leave a comment