-
Lab 5: SQL injection UNION attack, retrieving data from other tables
Problem Statement : ************************************************************************************************** This lab contains an SQL injection vulnerability in the product category filter. The results from the query are returned in the application’s response, so you can use a UNION attack to retrieve data from other tables. To construct such an attack, you need to combine some of the techniques you learned…
-
Lab 4 : SQL injection UNION attack, finding a column containing text
Problem Statement : This lab contains an SQL injection vulnerability in the product category filter. The results from the query are returned in the application’s response, so you can use a UNION attack to retrieve data from other tables. To construct such an attack, you first need to determine the number of columns returned by…
-
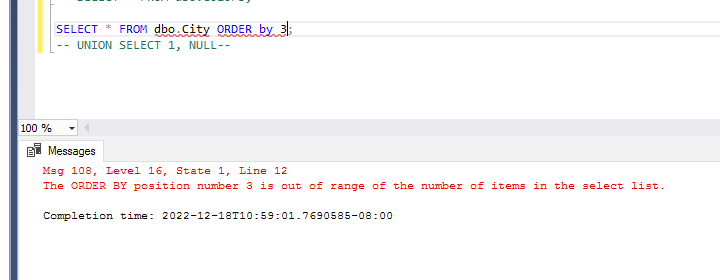
Lab 3 : SQL injection UNION attack, determining the number of columns returned by the query
Problem Statement : This lab contains an SQL injection vulnerability in the product category filter. The results from the query are returned in the application’s response, so you can use a UNION attack to retrieve data from other tables. The first step of such an attack is to determine the number of columns that are…
-
Understanding the UNION ATTACK
https://portswigger.net/web-security/sql-injection/union-attacks SQL injection UNION attacks When an application is vulnerable to SQL injection and the results of the query are returned within the application’s responses, the UNION keyword can be used to retrieve data from other tables within the database. This results in an SQL injection UNION attack. The UNION keyword lets you execute one or more additional SELECT queries and…
-
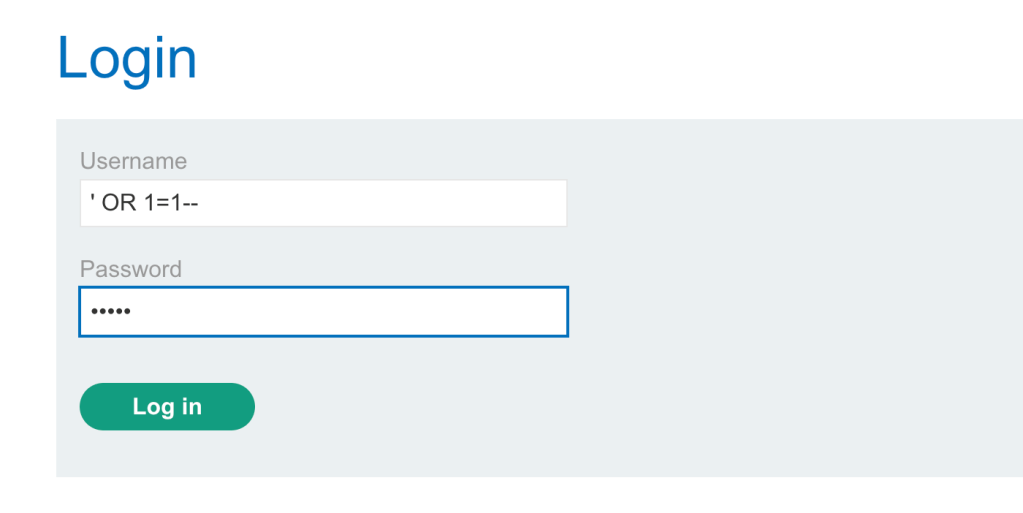
Lab 2 : SQL injection vulnerability allowing login bypass
Problem Statement : This lab contains an SQL injection vulnerability in the login function. To solve the lab, perform an SQL injection attack that logs in to the application as the administrator user. Access the lab Solution: Next – –> Type username as = ‘ OR 1=1– –> type any password Next I am logged in Understanding the Solution…